Today, networks are super crucial for organizations. But keeping them running smoothly can be challenging. That’s where VLAN comes in. They’re like magic tricks that help make LANs work better.
In this article, we’ll learn all about what VLANs are: what they are, how they work, and why they’re so awesome. We’ll also talk about the different kinds of virtual local area networks and how they can make LANs faster, safer, and more flexible. Ready to dive in?
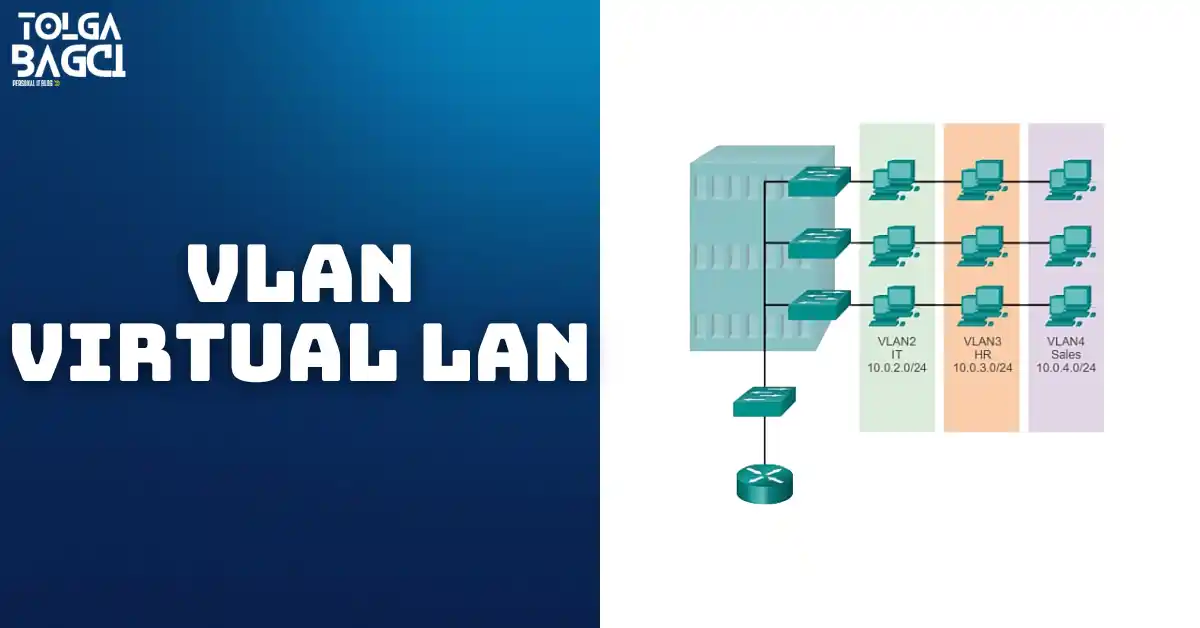
Credit: CiscoPress
Understanding VLANs: How Virtual Local Area Networks Make Networks Better
VLAN (Virtual Local Area Network) is super important for making organizations work better. It’s a tech thing that helps LANs run smoother by splitting big groups of computers into smaller ones.
Okay, so think about how networks are set up. You’ve got these devices called routers that control the traffic going through them. But routers can only handle so much traffic at once. Their main job is to send data between different areas, not to connect lots of devices.
That’s where switches come in. They’re like the traffic cops of local networks, helping devices talk to each other. Just like routers, they can also create these virtual local area LANs to make things run more efficiently.
So, basically, VLANs are like a secret weapon for designing networks. They help organizations meet their goals by organizing how devices connect and talk to each other. And guess what? Nowadays, virtual LANs are for more than just local areas. They can also help out with more extensive LANs, like ones that cover entire cities or regions.
What Does VLAN Do?
It’s like putting different teams into their rooms, even though they’re all in the same building. This helps organize who talks to whom and makes things more efficient. Instead of relying on where devices are plugged in physically, these use logical connections.
With VLANs, you can split up your network based on what different groups of devices do, like who’s working on which project or what applications they’re using. Each group acts like it’s on its LAN, even if they’re all using the same wires and stuff.
Every switch port can be part of a virtual LAN group, and messages only go to the devices in that group. This helps keep things tidy and prevents unnecessary traffic from clogging up the network. It’s like having separate rooms for different teams so they can work without bothering each other.
Also, these groups help with security. You can set restrictions for who can access which VLAN, adding an extra layer of protection to your network. Each switch port can only be connected to virtual LAN, except for exceptional cases, like when a port connects to a phone or another switch.
VLAN Advantages
Making sure employees can work well and that the company’s network can change as needed is super essential for a company to do well. These virtual LANs help set up networks that match what the company wants to achieve. Here are the main benefits:
- Security: Sensitive information is kept safe by keeping it separate from other parts of the virtual LAN. In the picture, the computers used by teachers are in VLAN 10, entirely apart from the data used by students and visitors.
- Cost reduction: Saving money happens because you don’t need to spend a lot on fancy LAN upgrades. Instead, you can make the most of what you already have, such as connections and how much data your network can handle at once.
- Better performance: Splitting flat areas into smaller groups helps stop too much traffic going around and makes things work better.
- Reduced broadcast areas: Breaking a LAN into the virtual local area reduces how many devices are all trying to talk at once.
- Higher efficiency of IT staff: It makes managing the virtual LAN easier because people who need similar things from the LAN are put together in the same group. When a new device joins, it automatically gets all the rules and settings set up for that group. Plus, it’s simple for IT folks to understand what each group is for just by looking at its name.
- Simpler management of applications and projects: These bring together devices and users based on where they are or what they’re doing for the company. This setup helps manage projects or use specific programs more efficiently. For instance, think about a unique online tool just for teachers to make lesson plans.
Each virtual LAN in a switched network is its neighborhood on the internet. When you’re setting up them, it’s a good idea to organize them in a particular order.
This way, each area of the network gets its unique address, and everything fits together neatly.
Types of Virtual Local Area Network
1. Data VLAN
A VLAN that handles regular stuff users do, like sending emails or browsing the internet. It’s common to keep phone calls separate from other internet activities. These groups help split the network into different groups of users or devices.
2. Default VLAN
When you first set up a switch with its basic settings, all the ports join a group called the default VLAN. This means they’re all in the same chatting space.
So, any device plugged into any port can talk to each other. In Cisco switches, this default group is called VLAN 1, and every port starts in it.
It works just like any other group, but you can’t change its name or get rid of it. It handles essential behind-the-scenes stuff for the network.
3. Native VLAN
An 802.1Q host port gets a particular group for itself called a local VLAN. Master link ports are like highways between switches and can handle traffic for lots of different groups.
The 802.1Q host port can deal with traffic that comes with tags (that’s like a label telling which group it belongs to) and traffic without tags. Untagged traffic goes into the local, which is usually VLAN 1.
These are there to make sure older devices can still talk with newer ones, even if they don’t use tags. This local area is a familiar signpost at both ends of a connection.
You should set up this type of network to work together with VLAN 1 and other groups, not on its own.
4. Management VLAN
Any VLAN set up to control how a network key is managed. Usually, virtual LAN 1 is the one used for management, but it’s not always the best choice because it’s the default.
To make this work, it gets its IP address and a unique switch interface that lets you control the switch using different tools such as HTTP, Telnet, SSH, or SNMP.
In older versions of the Cisco Switch 2960, only one switch interface was active for management. However, with newer versions of the Cisco IOS 15. x for Catalyst 2960 series switches, you can have more than one active interface for management.
However, having multiple local area network management might make your structure more vulnerable to attacks.
How Does VLAN Reduce Network Traffic?
VLANs are like sorting machines for LANs. They split an extensive network into smaller groups, which helps cut down on how much traffic flows through the LAN. This splitting process is called segmentation. A VLAN is made by gathering a bunch of devices and ports together, even if they’re not physically close.
With VLANs, messages only go to devices in the same group, which stops useless traffic from jamming up the network. Each group is its little broadcast area, so messages only travel within that area, only to some devices in the area. This means fewer devices are talking at the same time, which makes the LAN work better.
Also, splitting the LAN into smaller groups helps shrink the overall traffic in the area. That makes the LAN faster and more dependable. They also lower the amount of traffic that goes through each part of the LAN. When less traffic goes through, there’s less chance of the LAN getting all jammed up.
Conclusion
VLANs are really important for making them work well and stay safe. They split extensive LANs into smaller groups, which makes it easier to manage who’s doing what. This makes things run smoother, keeps important info safe, and makes managing projects and apps simpler.
Plus, it adds extra security by keeping sensitive stuff apart from the rest of the LAN. As networks keep growing and changing, virtual LANs will keep being super helpful for companies who want their LANs to run better, save money, and stay safe.